Introduction
Introduction
In today’s hyper-connected world, where billions of devices communicate and share data continuously, traditional security paradigms—especially password-based authentication—are rapidly becoming obsolete. According to recent industry reports, passwords remain the most exploited attack vector, responsible for over 80% of hacking-related breaches. As a response, the tech industry is shifting toward hardware-based security and cryptographic authentication models.
At the heart of this transformation are three key innovations:
-
Secure Elements (SEs) embedded in semiconductors for hardware-rooted trust.
-
FIDO2 Authentication, enabling phishing-resistant and passwordless logins.
-
The broader passwordless authentication movement, focused on eliminating user-created credentials.
This article explores each in-depth, showcasing their technical workings, industry applications, and strategic importance in building a secure digital future with secure elements, FIDO2 Authentication, and passwordless authentication.
What is a Secure Element?
A Secure Element (SE) is a physically isolated hardware component, purpose-built for performing cryptographic operations and securing sensitive data. It is designed to protect against both software and physical attacks, ensuring data confidentiality, integrity, and authenticity.

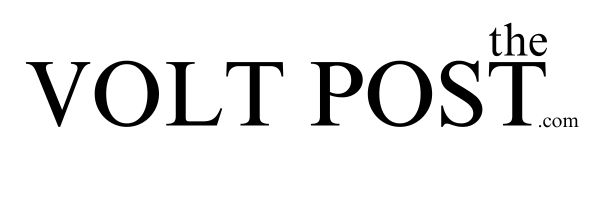
Core Functions of Secure Elements:
-
Cryptographic Key Management – Generation, storage, and handling of public/private keys.
-
Secure Storage – Non-volatile memory isolated from general-purpose processors.
-
Authentication – Device identity verification via secure certificate management.
-
Encryption & Decryption – Hardware-accelerated cryptographic processing.
-
Secure Boot & Firmware Updates – Ensures only verified software executes.
Security Attributes:
-
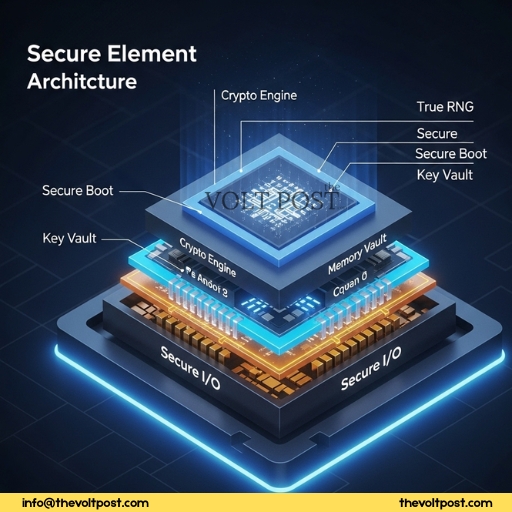
Isolation: Operates independently from the host OS and CPU, avoiding malware interference.
-
Tamper-resistance: Shields against side-channel, fault injection, and invasive physical attacks.
-
Certifications: Many SEs are Common Criteria (CC EAL4+) or FIPS 140-2 certified.
Architecture Overview:
Types of Secure Elements:
| Type | Description | Common Use Cases |
|---|---|---|
| eSE (Embedded SE) | Built into the SoC or module | Smartphones, IoT devices |
| SIM/UICC | Subscriber Identity Module with SE capabilities | Mobile networks, eSIMs |
| Discrete SEs | Standalone chips (e.g., NXP A71CH, Infineon) | Smart cards, secure USB tokens |
| TPM (Trusted Platform Module) | Standardized SE for PCs and servers | Endpoint integrity, BitLocker |
Importance of Secure Elements in Semiconductor Ecosystems
Secure Elements are critical enablers of security in modern semiconductor platforms—especially in sectors where privacy, trust, and resilience are paramount.
Semiconductor Integration:
-
IoT Chipsets – SEs embedded in microcontrollers or sensor nodes secure device identity and firmware.
-
Mobile SoCs – SEs facilitate biometric authentication (Face ID, fingerprint) and mobile payment (e.g., Apple Pay, Samsung Knox).
-
Automotive Semiconductors – SEs enforce OTA (Over-The-Air) update integrity and V2X communication security.
-
Edge AI Processors – Secure boot and model protection for ML inference at the edge.
Industry Benefits:
-
Zero Trust Architecture (ZTA): SEs form the hardware root-of-trust (HRoT) necessary for modern cybersecurity architectures.
-
Supply Chain Protection: Verify component authenticity at every stage.
-
Regulatory Compliance: Meets PCI-DSS, GDPR, HIPAA, and NIST mandates through hardware-level protections.
-
Long-Term Trust: Tamper-proof storage for 10–25 years in industrial environments.
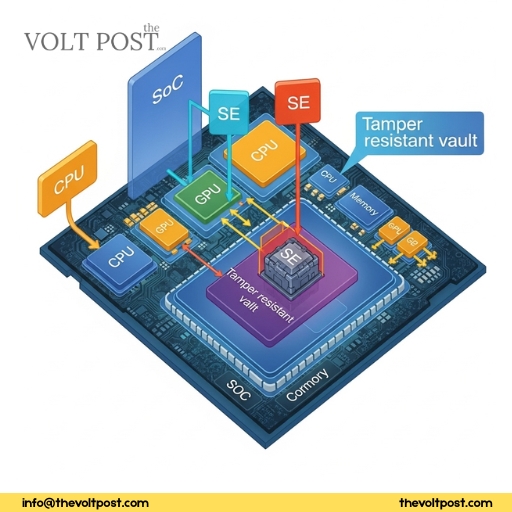
FIDO2 enables passwordless authentication by generating public-private key pairs locally on the device, never transmitting private data over the internet.
What is FIDO2 Authentication?
FIDO2 (Fast Identity Online 2) is a set of open authentication standards developed by the FIDO Alliance and W3C to enable secure, passwordless login using public key cryptography. It is a modern replacement for passwords and traditional two-factor authentication (2FA) systems.
Key Components of FIDO2:
| Component | Description |
|---|---|
| WebAuthn (Web Authentication API) | JavaScript API that allows browsers and websites to interact with authenticators |
| CTAP (Client to Authenticator Protocol) | Enables external authenticators (e.g., USB keys, smartphones) to communicate with clients |

Technical Workflow:
-
Registration Phase:
-
The user registers with a FIDO2-enabled service.
-
The authenticator generates a unique asymmetric key pair.
-
The private key is stored securely (typically in an SE).
-
The public key is sent to and stored by the server.
-
-
Authentication Phase:
-
The server sends a challenge to the client.
-
The authenticator signs the challenge with the private key.
-
The server verifies the signature with the public key.
-
This model ensures that user credentials never leave the device, and there’s no central database of passwords to hack.
Supported Authenticators:
-
On-device biometric sensors (e.g., fingerprint readers).
-
Hardware security keys (e.g., YubiKey, Feitian).
-
Trusted platform modules (TPMs) and secure enclaves.
-
Mobile phones acting as roaming authenticators.
Importance of Passwordless Authentication
Passwords are a major security liability due to:
-
Human fallibility: Reuse of weak passwords across sites.
-
Phishing attacks: Trick users into divulging credentials.
-
Database breaches: Compromised passwords leak to the dark web.
Passwordless Authentication Solves These Problems:
-
No shared secrets: Eliminates storage of passwords on servers.
-
Biometric assurance: Strong identity link between user and device.
-
Hardware-backed: Cryptographic operations done in tamper-resistant chips (SEs, TPMs).
-
Frictionless UX: No typing or remembering passwords.
Real-World Examples:
| Use Case | Passwordless Solution | Benefit |
|---|---|---|
| Microsoft 365 | Windows Hello + TPM | Phishing-resistant workplace logins |
| Google Accounts | Passkeys + Android SE | No password, no OTP |
| Banking Apps | Biometric + FIDO2 | SCA compliance in PSD2 |
| DevOps Access | SSH with FIDO2 keys | Secure, audit-ready shell access |
How Secure Elements Power FIDO2 and Passwordless Authentication
Secure Elements provide the secure execution environment needed for cryptographic key management in FIDO2 authentication. This ensures that:
-
Private keys cannot be extracted or duplicated.
-
Biometric templates are never exposed.
-
Cryptographic operations are shielded from malware and rootkits.
Integration Stack:
Vendor Implementations:
-
Apple Secure Enclave: Used for Face ID + passkeys.
-
Google Titan M2 SE: Secures Android device credentials and Google account logins.
-
Microsoft Pluton (TPM-in-CPU): Backs Windows Hello authentication.
Strategic Implications & Adoption Trends
Market Outlook:
-
The global passwordless authentication market is projected to exceed $50 billion by 2030, growing at a CAGR of over 15%.
-
Over 75% of Fortune 500 companies are actively testing or deploying FIDO2 solutions.
Leading Industries and The Adoption Drive:
-
Finance: PSD2 and open banking mandates require strong customer authentication (SCA).
-
Healthcare: HIPAA demands robust access controls for electronic patient records.
-
E-Government: Digital identity frameworks (e.g., India’s Aadhaar, EU eIDAS) rely on strong cryptographic systems.
-
Manufacturing & IoT: Device onboarding, firmware signing, and data integrity rely on embedded SEs.

Secure elements and passwordless technologies work in tandem to create an end-to-end trust chain—from device boot to cloud interaction.
Conclusion
The convergence of Secure Elements, FIDO2 authentication, and passwordless access models marks a profound evolution in how we design digital trust. As passwords fade into history, hardware-based security is taking center stage—offering resilience against phishing, malware, and insider threats.
For semiconductor makers, this means embedding security by design. For enterprises and governments, it means adopting standards-based authentication. And for end users, it promises a future that’s both more secure and far more user-friendly.

References:
-
FIDO Alliance Technical Overview: https://fidoalliance.org
-
NIST SP 800-63B Digital Identity Guidelines
-
Common Criteria Secure Element Protection Profiles
-
Microsoft Security Blog on Passwordless Future
-
Yubico White Papers on Hardware Security Keys

Secure elements and FIDO2 protocols are ushering in a new era of passwordless authentication—where trust is built into the hardware, not just software.